Information Security
Cyber Fusion Center: Driving Proactive Defense
Organizations attempting to respond to this complex environment often face or create additional challenges due to poor people, process, and technology decisions. Separations in both organizational boundaries, SOC shift structures, and integration and automation of processes inhibit collaboration and prevent rapid containment and resolution of cyber events.
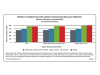
Improving Windows Client Performance and Security: An Impact Comparison of AC and Traditional AV
While traditional anti-virus (AV) solutions can provide protection for endpoints, constantly running AV processes with potentially frequent signature updates can consume resources that could otherwise be used to provide application services to users.
Top 5 Questions for a CISO
Thankfully, most organizations now have a Chief Information Security Officer. The CISO's primary function is to stand in the gap between the business and all the IT related risks that surround the modern-day organization. He or she may have a staff of trained security professionals, or perhaps your leader has engaged third party service providers for many of the necessary controls. Regardless, the CISO is the where 'the buck stops' when it comes to IT risk management.
Meeting Data Residency and Compliance Challenges in Global Enterprises
In today's global business environment, companies are increasingly finding their employees, business practices, and IT systems stretched across international boundaries. However, one element of a global enterprise remains surprisingly local: how to effectively manage data residency requirements and data privacy regulations.
Data Sheet: Voltage SecureData Suite for Test/Dev
Generating data for test and development environments presents serious challenges for enterprise security and risk management. When data is copied from production databases and used directly for test/development, large volumes of private data accumulate on unprotected servers and workstations. The use of outsourced and offshore QA and development services further increases the risks. An alarming number of data breaches, along with complex regulatory compliance requirements, highlight the need to de-identify sensitive data when moving from production to test, development, and training environments.
TRUSTe 2014 US Consumer Confidence Privacy Report
As part of our commitment to helping companies to safely collect and use consumer data to power their businesses, we wanted to get behind the headlines and find out what effect the events of 2013 have had on consumer privacy concerns and provide an accurate picture of the potential impact this could have on businesses in the year ahead.
Catbird vSecurity
Catbird vSecurity is an integrated network security solution purpose-built for virtualized infrastructure with continuous monitoring, automated enforcement, and real-time proof of compliance capabilities that accelerate virtualization and dramatically increase operational efficiencies.
SEC Cybersecurity Guidance… Critical Disclosure Considerations
SEC Cyber Risk Guidance Overview and SEC Cyber Risk Disclosure Issues.
Case Study: A Leading Financial Services Organization Enables Threat and Vulnerability Management
Overview: As business operations scale up and become increasingly dependent on Information Technology (IT), IT environments will continue to become more complex, exposing organizations to a wide array of risks, threats, and vulnerabilities that have a direct impact on the performance of the enterprise.
Streamlining Information Protection Through a Data-centric Security Approach
This document introduces a unique approach from Voltage Security that combines data encryption and masking technology in one, which can vastly simplify data privacy, whilemitigating data leakage at a fraction of the cost of prior approaches. One fundamental technology is Voltage Security's Format-Preserving Encryption (FPE), which for the first time, allows encryption 'in place' in databases and applications, without significant IT impact.
Use Case Brief: Ensuring Privacy for PII and PHI in Regulated Industries
Competing encryption offerings we looked at would have required us to hire three or four dedicated administrators to keep everything running smoothly. Voltage SecureMail can be managed with our regular email administrative staff, saving us a lot of time and money.
Voltage Customer Success Story - Regional Air Carrier
A growing regional air carrier needed a way to protect its customer data and achieve compliance at both level-1 and level-2 classifications. The Voltage Security solution combines the following technologies to deliver a simple and cost-effective solution across the entire company: Voltage Secure Stateless Tokenization (SST) technology, Voltage Format-Preserving Encryption (FPE), and Voltage Page-Integrated Encryption (PIE).
End-to-end Data Protection for the Way Your Business Works
Voltage SecureData Enterprise brings a unique, proven data-centric approach to protection – where the access policy travels with the data itself – by permitting data encryption and tokenization without changes to data format or integrity, and eliminating the cost and complexity of issuing and managing certificates and symmetric keys.