Webinars:
Cyber Risk Quantification: Turning the Dream into Reality
Recorded: July 14 | 2022 Attend
Cyber Risk Quantification can help CISOs financially quantify risk for senior executives, identify program gaps, and prioritize areas for improvement. Unfortunately, despite the obvious benefits, many CISOs are struggling to implement cyber risk quantification (CRQ)
Top Regulatory & Compliance Trends Impacting Risk Management
Recorded: July 28 | 2022 Attend
The COVID-19 pandemic and increased geopolitical uncertainty has placed new priorities and responsibilities on the shoulders of risk and compliance professionals. Executives have realized that stronger ERM programs are required to remain competitive in this new era. Risk leaders, in turn, are looking beyond the urgent ERM measures required to handle the pandemic to how an effective enterprise risk management program can be a competitive differentiator for their companies.
Understanding the Modern Attack Surface: IoT and Supply Chain Risk
Recorded: October 6 | 2022 Attend
The corporate attack surface is rapidly expanding: how can security professionals get ahead of the curve and create resilient organizations?
Aligning Cybersecurity Best Practices with Third-Party Risk
Recorded: February 16 | 2023 Watch Now
The cyber threat landscape grows exponentially each year. Third-party cyber data breaches like the Kaseya data breach, a cyberattack that affected over 1,500 organizations, have prompted regulators to raise cybersecurity standards. In the United States, the Biden Administration aims to improve nationwide cybersecurity with an executive order. The 100-day plan aims to modernize federal infrastructure, improve supply chain security, establish a cybersecurity review board and more.
How to Effectively Communicate Cybersecurity Risks to the Board
Recorded: August 25 | 2022 Attend
It has always been challenging for security leaders to communicate the value of cybersecurity investments to board. Giving transparency about the weakness of organizations can be pretty uncomfortable but, it is essential to increase the Cybersecurity level. As an IT Manager, CISO, or CSO, your understanding of risk and compliance is intimate and understood in infosec terminology. You must offer board executives a set of data to help them make informed decisions based upon the optimal management.
Enriching Third-Party Risk Processes with Targeted Risk Intelligence
Recorded: October 20 | 2022 Attend
With organizations having an average of over 5500 third parties in their vendor ecosystem, third-party risk management (TPRM) can be overwhelming and costly. Manual approaches to TPRM research and analysis are no longer appropriate. Targeted risk intelligence and automated data feeds can enable organizations to recognize risk sooner and respond with increased operational resilience, reducing the manual burden and cost.
Streamlining GRC Controls to Optimize Cybersecurity
Recorded: November 17 | 2022 Attend
In today’s interconnected world of rapid data exchange, GRC Controls impact each and every part of an organization’s cybersecurity posture.
Utilizing the NIST Framework for Full-Cycle Privilege Orchestration
Recorded: September 8 | 2022 Attend
A huge percentage of data breaches start with privileged credential abuse. There are often many privileged accounts that today’s overburdened IT security teams lose track of them. Stop leaving privileged accounts available for attackers to compromise and insiders to misuse! Instead, discover and remove them to achieve zero standing privilege (ZSP).
Data Privacy Essentials
Recorded: November 3 | 2022 Attend
Data privacy is a key component in many strict regulatory mandates and a subject of increasing attention from the public at large. To avoid steep fines and attract and retain customers, organizations must ensure the privacy of all the sensitive data they process and store. But what's the best path to achieving that goal?
Navigating the Impacts of Your Security Performance on Cyber Insurance
Recorded: January 26 | 2023 Watch Now
The state of cybersecurity feels volatile. Despite massive worldwide spending on risk management to the tune of $150 billion, cyber attacks keep happening. Ransomware attacks doubled in 2021, with average ransomware recovery costs doubling to $1.85 million and average downtime increasing to 22 days.
Preparing for Ransomware with the NIST Cybersecurity Framework
Recorded: September 22 | 2022 Attend
Ransomware is a type of malicious attack where attackers encrypt an organization’s data and demand payment to restore access. It disrupts or halts an organization’s operations and poses a dilemma for management: pay the ransom and hope that the attackers keep their word about restoring access and not disclosing data, or do not pay the ransom and restore operations themselves. The methods used to gain access to an organization’s information and systems are common to cyberattacks more broadly, but they are aimed at forcing a ransom to bepaid.
How to Utilize Security Ratings in Third-Party Risk Management
Recorded: December 14 | 2022 Attend
In an interconnected, ever changing digital world, how well your data is secured across your supply chain is a matter of great importance. Failing to adequately screen vendor security risks can lead to data breaches, which can shut down operations, damage customer trust and incur hefty regulatory penalties.
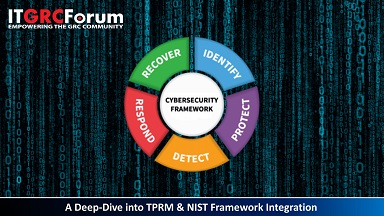
A Deep-Dive into TPRM & NIST Framework Integration
Recorded: April 20 | 2023 Watch
The National Institute of Standards and Technology (NIST) Cybersecurity Framework (CSF) is one of the leading frameworks for private and public sector cybersecurity maintenance and used by organizations of all sizes. The Framework helps to secure information systems and guide key decision points about risk management activities through the various levels of an organization from senior executives, to business and process level, and operations.