White Paper - Top 10 Database Threats
Practical applications for Big Data have become widespread, and Big Data has now become the new "prize" for hackers. Worse, widespread lack of Big Data security expertise spells disaster. These threats are real. This whitepaper explains common injection points that provide an avenue for attackers to maliciously access database and Big Data components.
TCS Enterprise Security & Risk Management: GRC Capabilities and Success Stories
GRC Capabilities and Success Stories from multiple vendors. Features ESRM Service offerings, GRC Exeprtise and implementation success stories with MetricStream and RSA Archer.
Managing Technological Change with Booz Allen Hamilton
Technology is a powerful force, enabling efficient corporate enterprise growth when properly employed. The pace of "new" continues to accelerate, posing both new opportunity and possibly massive disruption within our established systems and data. As in the case with other change elements—environmental, political, legislative— savvy corporate boards will have the pulse on emerging technology and a view as to when is the ideal timing to drive adoption for maximum benefit without wasting limited capital. Following are seven questions proactive directors should consider when "talking tech" with their management teams.
TCS Business Continuity Management
Client Organization [hereafter referred to as "the Bank"] was launched in 2007, as the investment banking arm of the largest bank in Kingdom of Saudi Arabia (KSA), to provide investment banking services to individual, institutional and corporate clients in the KSA. Underpinning this ethos is a fundamental belief that combining innovation with solid best practice service and execution will ensure that the Bank continues to be a first choice provider in its areas of strength.
Risk Monitor – Proactive governance Risk Management
Active governance goes beyond general oversight to ensure alignment and interlock strategy, through policy, procedures and roles in the operational fabric of the organization and carries through to suppliers, customers and third parties. By starting with these core aspects of active governance, you are in your way to creating a competency of proactive risk intelligence in your organization.
TCS Third Party Vendor Risk Assessment
The primary objective of any financial institution is to protect Confidentiality, Integrity and Availability (CIA) of business data and provide effective services to their customers and maintain long term customer relationship.
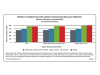
Improving Windows Client Performance and Security: An Impact Comparison of AC and Traditional AV
While traditional anti-virus (AV) solutions can provide protection for endpoints, constantly running AV processes with potentially frequent signature updates can consume resources that could otherwise be used to provide application services to users. Tolly evaluated the impact on client resources of Lumension AV solution and its alternative application control solution and compared it with traditional AV solutions from Symantex Corp, and McAfee, Inc. Understand how endpoint performance was affected and how effective they were against zero-day threats.
Targeted Threat Protection for POS Systems
Targeted attacks on retail Point of Sale (POS) networks have entered the scene in a big way recently, ushering in what could be the most damaging cyber-crime