Information Security
How to Mitigate the Unique Risks of Work From Home-Remote Office Networks
Recorded: July 15 | 2020 Attend
In response to the COVID-19 pandemic, more employees are working from home than ever before, introducing corporate devices to a variety of new and evolving vulnerabilities. We recently examined the data we routinely collect from Internet traffic to learn more about how this unprecedented shift to remote work changed the security landscape — and the results were alarming.
Privacy in a Pandemic: Implementing a Global Framework for Compliance
Recorded: July 30 | 2020 Watch Now!
In response to the Coronavirus Pandemic, countries are turning to tech to find solutions for containing the spread of the virus. New government initiatives including contact tracing apps are being implemented at lightning speed, and tele-health regulation is being approved in days instead of years. The world is rapidly digitising in response to all users working from home simultaneously, companies are adding network technology to expand coverage and capability, and online video conferencing is exploding.
Ransomware: How to Reduce Your Likelihood of Being a Victim
Recorded: September 16 | 2021 Watch
Colonial Pipeline. JBS meat processor. Scripps Health. The list of recent high-profile ransomware victims is long and growing. So are the costs to recover from these crimes.
CCPA 101: What is It, and How Will It Impact Your Organization?
Recorded: October 3rd | 2019 Attend
The California Consumer Privacy Act goes into effect January 1, 2020. If you are a for-profit company operating in the state of California, you need to have the right processes in place to support CCPA privacy requirements – or face stiff penalties. Are you ready?
Accelerating Threat Detection with Real-Time Security Intelligence
Recorded: October 22 | 2020 Attend
Many organizations rely on governance, risk, and compliance (GRC) technology to consolidate risk information from internal sources (such as finance, IT, and operations) and external sources to understand their threat landscape. Yet as vendor ecosystems grow in size and complexity, risk management teams are increasingly struggling to procure and maintain high-quality, real-time data to feed their GRC systems.
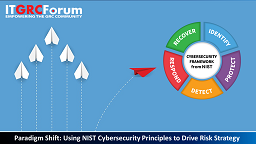
Paradigm Shift: Using NIST Cybersecurity Principles to Drive Your Risk Program
Recorded: November 16 | 2021 Watch
Cybersecurity risks come in many forms, and most importantly, risks are evolving at an increasingly rapid pace. Organizations across industries should work to implement adaptive cybersecurity processes that enable them to predict, prepare and react to the shifting landscape of cyber threats. The NIST Cybersecurity Framework enables organizations to apply the principles and best practices of security to drive risk management and protect against constantly advancing cyber attacks.
Cornerstones to Fortify Your Enterprise Cybersecurity Defense
Recorded: January 23 | 2020 Attend
The enterprise cybersecurity landscape is dramatically expanding in scale and complexity, and cyberattacks are growing in magnitude and impact as digital transformation increases on a global scale. From phishing scams, to ransomware attacks, to malicious breaches from state actors, the potential threat to your business is huge. According to the Ponemon Institute, the average per breach cost to a company in 2018 was estimated at $3.86 million, an increase of 6.4 percent over the previous year.
Executive Tips to Present Cybersecurity to the Board
Recorded: November 19 | 2020 Watch Now
Cyberattacks can cost an organisation its reputation, its customers and a great deal of money, making CEOs and board members more accountable. Yet, research shows that a high percentage of corporate boards are not actively involved in cybersecurity oversight. Nonetheless, Gartner estimates by 2021, 100% of large enterprises will be asked to report to their board of directors on cybersecurity and technology risk at least annually.
How to Improve Threat Intelligence with Advanced Analytics
Recorded: February 3 | 2022 Watch
Keeping track of cyber threats isn’t easy. The sheer volume of information threat researchers must sift through makes it difficult to collect, analyze, and research that data on time. The key to success is leveraging advanced analytics. It has been estimated that it would take 8,774 analysts working full time for a year to process the same amount of security event data that advanced analytics can process in that same time frame. Advanced analytics takes you from simply monitoring cyber security threats to active threat analytics, management, and prevention.
A CCPA Vs GDPR Comparison Guide for CCPA Readiness
When: April 30 | 2020 Attend
The groundbreaking California Consumer Privacy Act has been nicknamed California's GDPR, referring to the European Union's comprehensive data protection law that took effect in May 2018, just one month before the CCPA was passed. The CCPA, which comes into effect in January 2020, creates sweeping new rights for Californians and onerous transparency and other obligations for businesses handling their information.
Applying Threat Intelligence to Drive Control Assurance and Effectiveness
Recorded: February 25 | 2021 Attend
The frequency and severity of security incidents has risen as cyber criminals continually adapt their methods of attack to maximize profit, from mass-market approaches, to compromising as many organizations as possible, to more sophisticated attacks that target specific companies. This is why building an IT security strategy that has data-driven threat intelligence (TI) at its core is so critical.
Ransomware Attacks: Trends & Compliance Lessons Learned
Recorded: March 10 | 2022 Watch
The average ransom fee requested increased from $5,000 in 2018 to around $200,000 in 2020*, and according to FBI Director Christopher Wray, reports of ransomware attacks have tripled over the past year. The increased frequency and scope of these attacks present not only a business risk for a company, but legal and compliance risks as well.
Implementing a NIST Framework for Adaptive Cybersecurity
When: March 21 | 2019 Attend
In an age where cybersecurity threats are an everyday fact of life, organizations are looking for solutions that enable them to predict, prepare and react to the shifting landscape of cyber threats, and implementation of adaptive cyber security strategies is becoming inevitable to achieve that goal.